FortiAP wireless point to point bridge
- Matt Sherif

- Mar 26, 2019
- 3 min read
Updated: Apr 2, 2019
Sometimes you need connectivity in hard to reach places, whether it's too long of a run for copper ethernet, fiber being too costly, or any other number of factors. Point is, you need to extend connectivity somewhere and your best option is a wireless bridge. In this post we'll cover how to do this using Fortinet's FortiAPs.

While available online, the resources I used to set this up are scattered, so my goal here is to help streamline the process of creating a point to point bridge.
Equipment used in this lab:
- 1 x FortiAP S421E (Mesh Root Node) running v6.0,build0044,180920
- 1 x FortiAP S221E (Mesh Leaf Node) running v6.0,build0044,180920
- 2 x FortiGate 301E in HA mode running FortiOS 6.0.2
- 2 x FortiSwitch 224e-POE (1 for the root side, and one for the far side) running v6.0.2,build0046,181102
Assumptions
Bridge switch is already configured with L3 FortiLink
Vlan interfaces already created on root FortiSwitch
Topology

The topology in this example is relatively simple, but the challenge for this particular case was the distance being unsuitable for copper ethernet, and the expense of extending fiber.
Configuring the Mesh Root AP
In a wireless mesh network a Root AP is any AP with a hardwire uplink, serving as a connection point for any downstream APs. In the drawing above, the FortiAP S421E is the root node.
You can connect the AP to your FortiGate managed switch directly or you can pre-authorize it by adding it to the AP to the list of Managed FortiAPs by going to WiFi & Switch Controller > Managed FortiAPs > Create New. In this case I will allow the AP to be discovered by my fortigate.
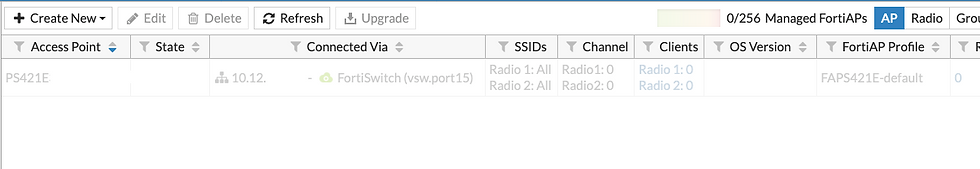
Select the AP and authorize it:

Now that the Root AP is authorized, I will click "Edit" and give it the friendly name of uv.mesh.root.
My next step is to create the Mesh SSID, in this case I have chosen to name it uv.mesh and I set the password. I've accepted the defaults for everything else.

I'll now go to FortiAP profiles, and clone the default profile for the S421. I do this so that any changes I make to that profile don't get applied to the default. Also, because of the distance of this link, we'll want to use the 2.4G antenna. The new profile will be UV FAPS421E.

I highlighted Radio 1 here, because the only change made was to the SSIDs, I want to dedicate this to uv.mesh. I have also enabled HTTPS and SSH access.
Now we'll apply the profile by going back to ManagedFortiAPs, right click on the uv.mesh.root AP

Now the Mesh Root AP is all set up. Time to configure the Mesh Leaf.
Configuring the Mesh Leaf
In this scenario, the customer had already mounted the AP, so plugging the leaf AP into the FortiGate and authorizing the same way was a no go. I did however have cli access to the AP.
Once logged into the AP issue the following commands - replace these values with your own
cfg -a MESH_AP_TYPE=1
cfg -a MESH_AP_SSID=fortinet.mesh.root
cfg -a MESH_AP_PASSWD=hardtoguess
And wait - in about 5 minutes you will see the mesh leaf pop up under Managed FortiAPs:

Once the AP is authorized, clone the default S221E profile, rename the cloned profile and add the mesh SSID to the 2.4 GHz radio. Then add the following configuration to bridge the VLANs across the link
Update: the APs appear to be able to pass the VLANs by default, only use MESH_ETH_BRIDGE_VLANS variable if you need to specify which VLANs to bridge, or if you encounter trouble using the defaults.
cfg -a MESH_ETH_BRIDGE=1
cfg -a MESH_ETH_BRIDGE_VLANS=100,200,300
cfg -c
reboot
For more information on the FortiAP cli click here.
Verification
Configure a number of ports with the different VLANs on the remote end and verify that devices in each respective VLAN are able to connect to network resources. In my case google came up.
And there you have it! We have a layer 2 Mesh bridge passing the requisite VLANs for traffic segmentation.



Comments